Dictate code. Ship faster.
Wispr Flow understands code syntax, technical terms, and developer jargon. Say async/await, useEffect, or try/catch and get exactly what you said. No hallucinated syntax. No broken logic.
Flow works system-wide in Cursor, VS Code, Windsurf, and every IDE. Dictate code comments, write documentation, create PRs, and give coding agents detailed context- all by talking instead of typing.
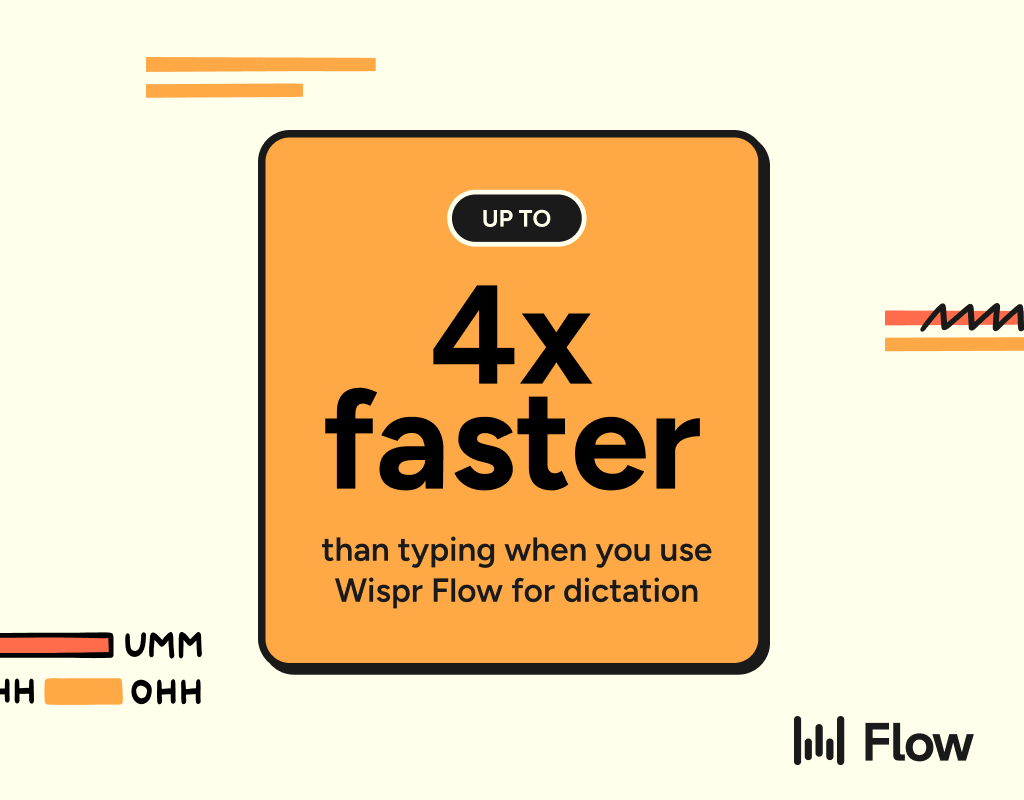
89% of messages sent with zero edits. 4x faster than typing. Millions of developers use Flow worldwide, including teams at OpenAI, Vercel, and Clay.
Available on Mac, Windows, iPhone, and now Android - free and unlimited on Android during launch.
Let me ask you something.
When a company gets hacked, where do you think the attack usually starts?
It rarely starts in the data center.
Most of the time, it starts at the endpoint.
A laptop. A desktop. A mobile device. A remote employee’s computer.
That’s why endpoint security is one of the most important concepts in cybersecurity today. Endpoint security simply means protecting every device that connects to a company’s network. Think of it this way: every laptop is a door. Every mobile device is a door. Every remote machine is a door. And if those doors aren’t locked properly, someone will walk in.
During my corporate career, I’ve seen incidents where one infected laptop created massive disruption. One employee clicked a phishing email. Malware was installed. Within minutes, the system started communicating with an external command server. Luckily, endpoint protection detected abnormal behavior and isolated the machine. That is endpoint security in action, and it’s often the difference between a small incident and a full-blown crisis.
Endpoint security today is not just antivirus. In 2026, it includes multiple layers: antivirus and anti-malware, Endpoint Detection and Response (EDR), behavior monitoring, device control, patch management, and encryption. Modern tools don’t just look for known viruses. They analyze what the device is doing. If a process suddenly starts encrypting hundreds of files, that’s suspicious. If a system starts communicating with unknown IP addresses, that’s suspicious. And the system can react automatically: isolate the device, alert administrators, and block malicious processes. That’s the difference between old security and modern endpoint security.
In cybersecurity interviews, companies often ask: “How would you secure endpoints in an enterprise?” A strong answer includes the fundamentals: regular patching, least privilege access, endpoint monitoring tools, user awareness training, and device encryption. Because security isn’t only about tools. It’s also about process and awareness. Tools reduce risk, but people and process determine outcomes.
There’s a quote often attributed to Alexander the Great: “I’m not afraid of an army of lions led by a sheep; I’m afraid of an army of sheep led by a lion.” In cybersecurity, leadership matters. If leadership takes endpoint security seriously, the organization becomes stronger. If leadership ignores it, even the best tools won’t be enough.
Let me simplify the idea. Endpoint security protects devices. Devices are entry points. Entry points are targets. Protect the endpoints, and you reduce your risk significantly.
In 2026, remote work has expanded the attack surface. Employees work from home, coffee shops, airports, and everywhere in between. The traditional network perimeter is no longer the main boundary. Now every endpoint is the new perimeter. If you understand that clearly, you understand modern security.
Endpoint security is not optional. It is foundational. And if you’re planning a career in cybersecurity, this is a concept you must master. Because attacks don’t start in theory. They start on devices. And protecting devices protects the organization.